All Posts - Category: Notes from the Field

Notes from the Field
10 MIN READ
Security Abuse of Misconfigured Active Directory Certificate Services Continue
by Eleanor Barlow • Jan 2025
Notes from the Field
6 MIN READ
What is an Endpoint Detection & Response (EDR) Silencer?
by Eleanor Barlow • Oct 2024

Notes from the Field
10 MIN READ
Resurgence in Lumma Stealer Malware Campaigns – Notes from the Field
by Eleanor Barlow • Oct 2024

Notes from the Field
5 Min READ
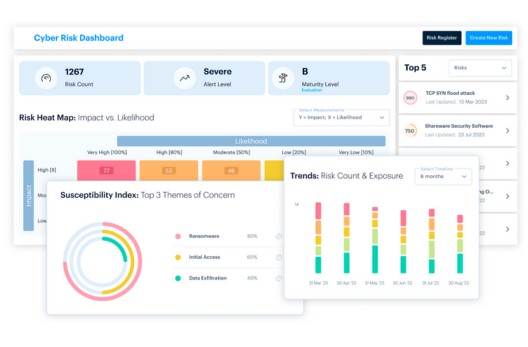
Notes from the Field. The Value of Log Management to Prevent Risks
by Eleanor Barlow • Jun 2024
Notes from the Field
10 MIN READ
Defend Against Social Engineering Campaigns Leveraging Typosquatting
by Eleanor Barlow • Feb 2024

Notes from the Field
10 MIN READ
Malicious ISATAP Tunneling Unearthed on Windows Server
by Eleanor Barlow • Jan 2024
Notes from the Field
10 MIN READ
Rising Cyber Threats in the Middle East – A Virtual Battleground
by Patrick McAteer • Nov 2023
Notes from the Field
10 MIN READ
Mitigating Session Hijacking via NetScaler Citrix Bleed Vulnerability
by Eleanor Barlow • Nov 2023